Ledger warned that post-quantum cryptography designed to withstand assaults from quantum computer systems may really be susceptible. {hardware} shouldn’t be protected. This alert went viral on April 29, 2026 after demonstrating that the personal key might be extracted with out breaking the algorithm.
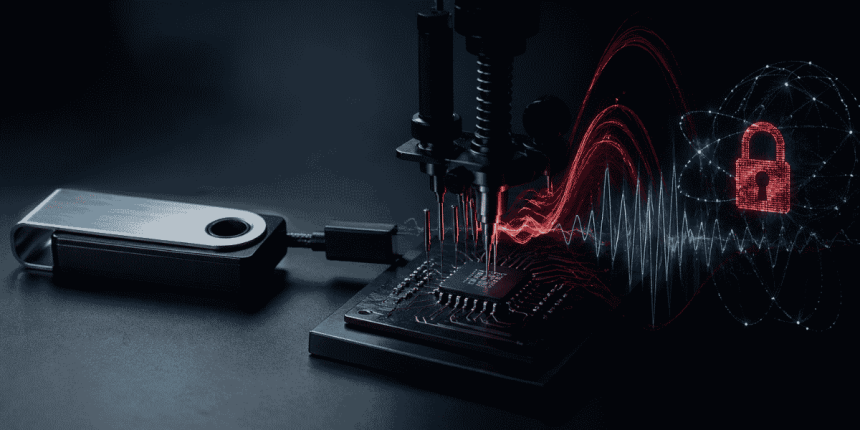
This threat is because of so-called side-channel assaults (facet channel assaultSCA), This can be a methodology that’s not concerning the arithmetic of encryption, however about its execution. As a substitute of cracking the system, attackers observe oblique alerts equivalent to energy consumption and electromagnetic emissions from the chip because it processes information. From these bodily “leakages” it’s attainable to deduce delicate data equivalent to personal keys.
Based on Ledger’s Donjon crew, such a assault is already attainable in sensible implementations of post-quantum cryptography. In checks run on a model open supply ML-KEM algorithm (previously often known as Kyber), They had been capable of get well a part of the personal key utilizing about 40 electromagnetic measurements. This course of will full inside 1 minute.
As reported by CriptoNoticias, ML-KEM (Modular lattice-based key encapsulation mechanism) is a just lately standardized algorithm inside post-quantum cryptography. It’s designed to safe key alternate even in opposition to quantum computer systems, primarily based on a mathematical drawback that’s thought of troublesome to resolve. however, Ledger’s experiments confirmed that theoretical energy doesn’t forestall bodily implementation from leaking data.
The impression is direct. gadgets like {hardware} pocketsGood playing cards, IoT techniques, and even cell phones may be compromised if an attacker has bodily entry and the mandatory gear to measure these alerts. On this situation, safety doesn’t solely rely upon the algorithm, but in addition on how the algorithm is applied. {hardware}.
To scale back this threat, Factors out the necessity to incorporate particular measures for leisure. Amongst them, essentially the most distinguished one is masking (masking), splits the important thing into random elements. he shufflingchange the order of operations. The opposite is asynchronous, which ends up in variable execution occasions. These strategies intention to make correlation between the bodily sign and the processed information troublesome.
This caveat brings vital nuance within the transition to post-quantum cryptography. It isn’t sufficient to have algorithms which are proof against quantum computing. True safety is determined by working in an atmosphere designed to keep away from bodily publicity. In follow, which means customers and companies want to guage not solely what cryptography to make use of, but in addition what sorts of gadgets and below what circumstances the cryptography can be applied.